Troll 3 CTF Walkthrough
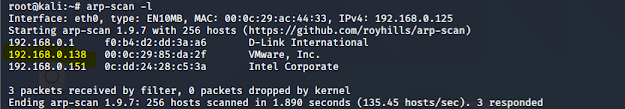
Troll 3 CTF Walkthrough In this article we will see a walkthrough of the Tr0ll 3 virtual machine. Tr0ll 3 Details Download Tr0ll 3: https://www.vulnhub.com/entry/tr0ll-3,340/ VM Description The latest version of the Tr0ll series. This one is a little different from the previous iterations, I would say still on the beginner++ level. I hope everyone has fun, be sure to tag @Maleus21 with screen shots of the flag. You will need to login with start:here Type: Boot 2 Root Goal: Obtain flag.txt Difficulty: Beginner++ Fun level: Over 9000 Penetration Methodology: l Network Scanning (Nmap, netdiscover) l Msf console l Aircrack-ng tool l Lynx : Lynx is a popular terminal based web browser on all flavors of Linux and it displays plain ASCII text on your terminal. l SSH login l Privilege Escalation l Get root access l Capture the flag L et’s try to find the IP of this machine using arp-scan or ne...

